Golang binaries are a bit hard to analyze but there are some tricks to locate the things and view what is doing the code.
Is possible to list all the go files compiled in the binary even in an striped binaries, in this case we have only one file gohello.go this is a good clue to guess what is doing the program.
On stripped binaries the runtime functions are not resolved so is more difficult to locate the user algorithms:
If we start from the entry point, we will found this mess:
The golang string initialization are encoded and is not displayed on the strings window.
How to locate main? if its not stripped just bp on [package name].main for example bp main.main, (you can locate the package-name searching strings with ".main")
And here is our main.main:
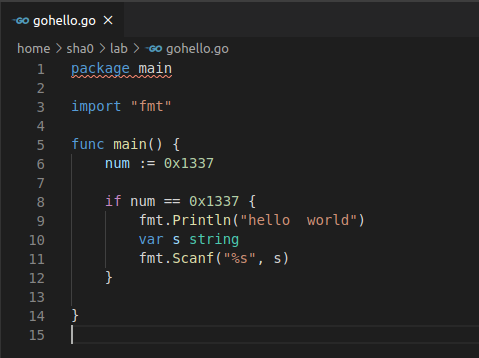
The code is:
So in a stripped binary we cant find the string "hello world" neither the initialization 0x1337 nor the comparator 0x1337, all this is obfuscated.
The initialization sequence is:
The procedure for locating main.main in stripped binaries is:
1. Click on the entry point and locate the runtime.mainPC pointer:
2. click on runtime.main function (LAB_0042B030):
3. locate the main.main call after the zero ifs:
4. click on it and here is the main:
The runtime is not obvious for example the fmt.Scanf() call perform several internal calls until reach the syscall, and in a stripped binary there are no function names.
In order to identify the functions one option is compile another binary with symbols and make function fingerprinting.
In Ghidra we have the script golang_renamer.py which is very useful:
After applying this plugin the main looks like more clear:
This script is an example of function fingerprinting, in this case all the opcodes are included on the crc hashing:
# This script fingerprints the functions
#@author: sha0coder
#@category fingerprinting
print "Fingerprinting..."
import zlib
# loop through program functions
function = getFirstFunction()
while function is not None:
name = str(function.getName())
entry = function.getEntryPoint()
body = function.getBody()
addresses = body.getAddresses(True)
if not addresses.hasNext():
# empty function
continue
ins = getInstructionAt(body.getMinAddress())
opcodes = ''
while ins and ins.getMinAddress() <= body.getMaxAddress():
for b in ins.bytes:
opcodes += chr(b & 0xff)
ins = getInstructionAfter(ins)
crchash = zlib.crc32(opcodes) & 0xffffffff
print name, hex(crchash)
function = getFunctionAfter(function)
Related articles
- Physical Pentest Tools
- Hacking Tools 2020
- Hacker Tools Software
- Android Hack Tools Github
- Hackers Toolbox
- Hack Tools
- Hacker Tools For Windows
- Hacking Apps
- How To Hack
- Pentest Tools Apk
- Hack Tools 2019
- Hacker Tools
- Hacking App
- Pentest Tools Framework
- Best Hacking Tools 2020
- Hacker Hardware Tools
- Hak5 Tools
- Pentest Tools Port Scanner
- New Hacker Tools
- Hacker Tools For Windows
- Pentest Tools Framework
- Hacker Tools Software
- Pentest Tools Find Subdomains
- Hacking Tools For Mac
- How To Install Pentest Tools In Ubuntu
- Hack Tools 2019
- Pentest Box Tools Download
- Easy Hack Tools
- Hacker Tools Software
- Hacking Tools For Mac
- Blackhat Hacker Tools
- What Are Hacking Tools
- Hack Tools For Pc
- Pentest Tools Android
- Hacking Apps
- Pentest Tools Download
- Pentest Tools Android
- Top Pentest Tools
- How To Make Hacking Tools
- Ethical Hacker Tools
- Hacking Tools For Windows Free Download
- Hacker Security Tools
- Pentest Tools Website
- Hacking Tools Software
- Physical Pentest Tools
- Computer Hacker
- Free Pentest Tools For Windows
- Hacking Tools Name
- Hacking Tools Windows
- Hackers Toolbox
- Hacker Tool Kit
- Hack Tools 2019
- Hacking Tools Online
- Hack Tools For Pc
- How To Install Pentest Tools In Ubuntu
- New Hacker Tools
- Android Hack Tools Github
- Tools For Hacker
- Pentest Tools Online
- Pentest Tools Website Vulnerability
- Hack Tools
- Pentest Tools Review
- Android Hack Tools Github
- Hacking Tools For Windows
- Pentest Tools Nmap
- Hacker Tools Free Download
- Hacking Apps
- Hacking Tools For Windows 7
- Pentest Tools For Android
- Pentest Box Tools Download
- Pentest Tools Website
- Hack Tools For Games
- Hack Tools Pc
- Ethical Hacker Tools
- Hack App
- Hacker Tools Windows
- Hacker Tools For Windows

















No comments:
Post a Comment